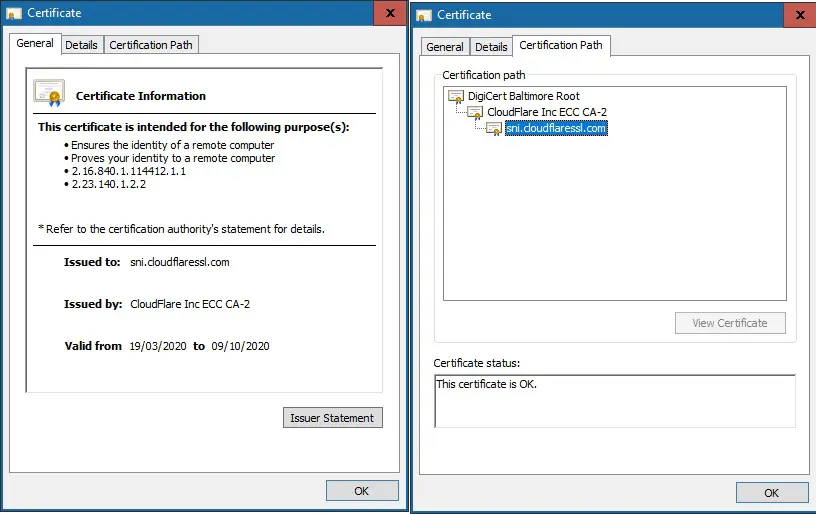
Usually, in the browser, by clicking the Lock icon, you can view the SSL certificate information.
And, we can also run the `openssl` command to view the server ceritifcate (e.g. SSL chain) on command line. For example:
$ openssl s_client -connect helloacm.com:443
CONNECTED(00000003)
depth=2 C = IE, O = Baltimore, OU = CyberTrust, CN = Baltimore CyberTrust Root
verify return:1
depth=1 C = US, ST = CA, L = San Francisco, O = "CloudFlare, Inc.", CN = CloudFlare Inc ECC CA-2
verify return:1
depth=0 C = US, ST = CA, L = San Francisco, O = "Cloudflare, Inc.", CN = sni.cloudflaressl.com
verify return:1
---
Certificate chain
0 s:C = US, ST = CA, L = San Francisco, O = "Cloudflare, Inc.", CN = sni.cloudflaressl.com
i:C = US, ST = CA, L = San Francisco, O = "CloudFlare, Inc.", CN = CloudFlare Inc ECC CA-2
1 s:C = US, ST = CA, L = San Francisco, O = "CloudFlare, Inc.", CN = CloudFlare Inc ECC CA-2
i:C = IE, O = Baltimore, OU = CyberTrust, CN = Baltimore CyberTrust Root
---
Server certificate
-----BEGIN CERTIFICATE-----
MIIE5TCCBIugAwIBAgIQC5UFOgyjwCAycwdYqx90XzAKBggqhkjOPQQDAjBvMQsw
CQYDVQQGEwJVUzELMAkGA1UECBMCQ0ExFjAUBgNVBAcTDVNhbiBGcmFuY2lzY28x
GTAXBgNVBAoTEENsb3VkRmxhcmUsIEluYy4xIDAeBgNVBAMTF0Nsb3VkRmxhcmUg
SW5jIEVDQyBDQS0yMB4XDTIwMDMxOTAwMDAwMFoXDTIwMTAwOTEyMDAwMFowbTEL
MAkGA1UEBhMCVVMxCzAJBgNVBAgTAkNBMRYwFAYDVQQHEw1TYW4gRnJhbmNpc2Nv
MRkwFwYDVQQKExBDbG91ZGZsYXJlLCBJbmMuMR4wHAYDVQQDExVzbmkuY2xvdWRm
bGFyZXNzbC5jb20wWTATBgcqhkjOPQIBBggqhkjOPQMBBwNCAATdjmNNRSTaJQRg
3DBHzEMpKUtoNzciod0FgETrfMpPmtFjqKTVBywJenDP2SBmrYozrn3TpL4dQ3/X
PARGh74No4IDCTCCAwUwHwYDVR0jBBgwFoAUPnQtH89FdQR+P8Cihz5MQ4NRE8Yw
HQYDVR0OBBYEFPoMno5zzaoue3G90nO8fnAOFWzCMD4GA1UdEQQ3MDWCFXNuaS5j
bG91ZGZsYXJlc3NsLmNvbYIMaGVsbG9hY20uY29tgg4qLmhlbGxvYWNtLmNvbTAO
BgNVHQ8BAf8EBAMCB4AwHQYDVR0lBBYwFAYIKwYBBQUHAwEGCCsGAQUFBwMCMHkG
A1UdHwRyMHAwNqA0oDKGMGh0dHA6Ly9jcmwzLmRpZ2ljZXJ0LmNvbS9DbG91ZEZs
YXJlSW5jRUNDQ0EyLmNybDA2oDSgMoYwaHR0cDovL2NybDQuZGlnaWNlcnQuY29t
L0Nsb3VkRmxhcmVJbmNFQ0NDQTIuY3JsMEwGA1UdIARFMEMwNwYJYIZIAYb9bAEB
MCowKAYIKwYBBQUHAgEWHGh0dHBzOi8vd3d3LmRpZ2ljZXJ0LmNvbS9DUFMwCAYG
Z4EMAQICMHYGCCsGAQUFBwEBBGowaDAkBggrBgEFBQcwAYYYaHR0cDovL29jc3Au
ZGlnaWNlcnQuY29tMEAGCCsGAQUFBzAChjRodHRwOi8vY2FjZXJ0cy5kaWdpY2Vy
dC5jb20vQ2xvdWRGbGFyZUluY0VDQ0NBLTIuY3J0MAwGA1UdEwEB/wQCMAAwggED
BgorBgEEAdZ5AgQCBIH0BIHxAO8AdQCyHgXMi6LNiiBOh2b5K7mKJSBna9r6cOey
SVMt74uQXgAAAXDz80rYAAAEAwBGMEQCIEl6oXM4EHydqzGMm8efrCUp4nEIaTKm
VbtHBTtarxxQAiBlhQ9R71vzf3M2M8UQEAN8yOVt0T5hl+Zb4yB+xDQ+UgB2APCV
pFnyANGCQBAtL5OIjq1L/h1H45nh0DSmsKiqjrJzAAABcPPzSyEAAAQDAEcwRQIh
AL4n31LbZn5nO+yXep4Kh0E4/4SMhpyBiOApVWLgWkjqAiBcWB6A4krBCl09ub8J
ttaFMV7+zPhjjTkt4toyrKu5iTAKBggqhkjOPQQDAgNIADBFAiAgA5xSHgF0Oa+f
dy8QoEUX7RCwTDQ+bSkfJ2A0JaAHBAIhAO6t2NuyqG8sLeEOEqj0L5Xqr72r4dRy
QpxHGpQRa3T7
-----END CERTIFICATE-----
subject=C = US, ST = CA, L = San Francisco, O = "Cloudflare, Inc.", CN = sni.cloudflaressl.com
issuer=C = US, ST = CA, L = San Francisco, O = "CloudFlare, Inc.", CN = CloudFlare Inc ECC CA-2
---
No client certificate CA names sent
Peer signing digest: SHA256
Peer signature type: ECDSA
Server Temp Key: X25519, 253 bits
---
SSL handshake has read 2507 bytes and written 394 bytes
Verification: OK
---
New, TLSv1.3, Cipher is TLS_AES_256_GCM_SHA384
Server public key is 256 bit
Secure Renegotiation IS NOT supported
Compression: NONE
Expansion: NONE
No ALPN negotiated
Early data was not sent
Verify return code: 0 (ok)
---
---
Post-Handshake New Session Ticket arrived:
SSL-Session:
Protocol : TLSv1.3
Cipher : TLS_AES_256_GCM_SHA384
Session-ID: 2369749FDF66D7BFD323F53958A27F6E45CDC2239A7FCDDCB1175A7C1C8B1466
Session-ID-ctx:
Resumption PSK: EEA87720335AD216961F713DB0544F8A7E5F42223DEB2DBA992483D24D75F60809373FF82BEFEA0692C248151CC2BDDE
PSK identity: None
PSK identity hint: None
SRP username: None
TLS session ticket lifetime hint: 64800 (seconds)
TLS session ticket:
0000 - 24 29 83 3e 7e 68 72 88-be fe 43 06 e6 91 6b 2e $).>~hr...C...k.
0010 - 98 32 0b c2 4f 6f 60 d0-6b 60 e0 40 8b c6 03 62 .2..Oo`.k`.@...b
0020 - 8f 8f 4c 25 ad 8c a1 22-c0 c7 47 94 5a 9e 97 18 ..L%..."..G.Z...
0030 - 81 eb 2f 4a b6 4c 07 02-aa e0 91 43 95 1e d2 22 ../J.L.....C..."
0040 - 6f 31 e5 2a 83 41 a1 6f-f9 ed 53 d2 0d 5d 89 cf o1.*.A.o..S..]..
0050 - 22 68 ad d9 bf 1d 49 b7-96 7f fc 09 6d 11 f5 f2 "h....I.....m...
0060 - 2a 5d a6 35 f0 fb 54 f5-be 1a d8 1d 19 ec 80 40 *].5..T........@
0070 - 57 15 cc a0 38 79 1d 47-34 75 81 73 77 ce ef d2 W...8y.G4u.sw...
0080 - e9 17 ee 66 63 d2 2f c6-29 ce 74 f0 62 1d 49 b2 ...fc./.).t.b.I.
0090 - bc c5 da 62 24 e3 42 97-b2 13 e2 97 ed 7c 2d dc ...b$.B......|-.
00a0 - d3 55 ac 3e 66 92 43 af-11 ba 41 60 66 c0 f4 f7 .U.>f.C...A`f...
00b0 - 74 4a 1b 7c dd d9 8d 21-9b fe a0 ae 3f 97 37 4b tJ.|...!....?.7K
00c0 - ef c5 d5 34 31 93 30 ab-9f 8b 8b 2d f5 3f 21 1f ...41.0....-.?!.
Start Time: 1595760329
Timeout : 7200 (sec)
Verify return code: 0 (ok)
Extended master secret: no
Max Early Data: 14336
---
read R BLOCK
---
Post-Handshake New Session Ticket arrived:
SSL-Session:
Protocol : TLSv1.3
Cipher : TLS_AES_256_GCM_SHA384
Session-ID: B126A49538D22C054CC7A61988EAB35538A7953C1516C98A52513E81C6245B73
Session-ID-ctx:
Resumption PSK: 16E0F2E582F4AF8120E79B33C54CA75E64FEFA6B8EF5CF819C59AEA63A0DBB96DE445563EF1D6C87028CE71BE1B5D137
PSK identity: None
PSK identity hint: None
SRP username: None
TLS session ticket lifetime hint: 64800 (seconds)
TLS session ticket:
0000 - 24 29 83 3e 7e 68 72 88-be fe 43 06 e6 91 6b 2e $).>~hr...C...k.
0010 - bb 07 3e 5b c8 33 49 bf-c4 23 d4 0b 29 04 c7 61 ..>[.3I..#..)..a
0020 - b9 63 d7 79 19 0d 00 55-fc 96 cc e4 2e d3 a5 d1 .c.y...U........
0030 - 86 91 13 e1 5d b7 91 ef-e0 ef 1b 3d ed eb e0 c3 ....]......=....
0040 - 74 a8 06 ce 03 8d 1e c0-a1 47 5e a1 94 3c 4c 60 t........G^..
--EOF (The Ultimate Computing & Technology Blog) --
Last Post: Algorithm to Shuffle String in Python3 According to Index
Next Post: How to Avoid Paying Too Much Fee when Cashing out Bitcoin via Wirex Credit Card?